Hi,
We would like to follow the Center for Internet Security (CIS) guidelines for OS hardening. Ubuntu Security Guide (USG) already implements those recommendations which makes a number of changes compared to the standard Ubuntu install. Has anyone successfully used/tried Ubuntu USG for a DHIS2 installation? are there any limitations we should be aware of?
Thank you!
Welcome back to the community! ![]()
Interesting post and question. I’ve FWD your question to @dhis2-security and if I receive any updates, I will let you know. I believe the response I got is that it’s being tested. If you test that as well, you’re welcome to post back your feedback and experience.
Thank you!
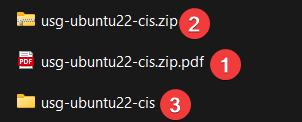
I’m attaching the Ubuntu USG reports we generated for our reference installation of DHIS2 on Ubuntu 22.04. The attached ZIP file (with PDF extension added to bypass the forum upload filter) contains HTML reports from the usg command.
usg-ubuntu22-cis.zip.pdf (444.0 KB)
I have mixed feelings of the entire CIS checklist:
- Some requirements do not cause harm but are practically useless (for example, “Modify the System Login Banner”).
- Requirements like in the section “Kernel Parameters Which Affect Networking” may theoretically impact performance or result in incompatibilities with other devices on the same network. Security benefits are very dependent on the specific implementation.
- Similar considerations apply to “Enable Randomized Layout of Virtual Address Space”. Although this option can eliminate some attack vectors, any changes outside the default setup on many Linux distributions may lead to weird, unpredictable, and faulty behaviour of software we run on top of the OS.
Dear Markevich,
I cannot open the pdf file. Please can you verify and resend file if it is not OK
After downloading the file, please rename the file by removing the .pdf and keep the name .zip so it will be the extension of the file.